Accelerate Cilium Adoption with
Advanced Observability and Deeper Insights
Maximize your cloud networking potential with Cilium, the leading Container Network Interface (CNI) known for its high-performance and adaptable eBPF-powered network management. Gloo Network for Cilium transforms complexity into simplicity, offering an integrated solution that streamlines Cilium’s onboarding, integration, and monitoring.
Gloo Network for Cilium’s best-in-class networking, scalability, and observability tools are perfectly suited for IPv4/IPv6 Kubernetes CNI, robust threat detection, and zero-trust policies. Benefit from world-class 24/7/365 enterprise support and heightened network visibility. As your needs evolve, seamlessly shift to service mesh technologies with Gloo Mesh integration, managed effortlessly through a unified console, enhancing operational simplicity and efficiency.
Gloo Network for Cilium is ...
Simplified
While upstream Cilium offers many advantages, mastering its full range of advanced features can be challenging. To help, Gloo Network for Cilium provides enhanced support and resources, easing Cilium's use in production environments. This approach simplifies onboarding, allowing enterprises to fully utilize Cilium's capabilities without being slowed down by technical complexities.
High Performance
Gloo Network for Cilium harnesses the power of eBPF technology to deliver exceptional performance, and observability for complex cloud-native infrastructures. It offers advanced support for IPv4/IPv6 Kubernetes CNI, ensuring efficient, secure data management across diverse network layers.
Deeper Insights
Gloo Network for Cilium simplifies network monitoring and management by combining metrics, logging, and tracing for a clear overview of network activities. It provides detailed insights into network operations, helping teams greatly reduce downtime and improve reliability. In addition, Gloo Network for Cilium provides users with effective management tools and troubleshooting features to keep the network running smoothly at all times.
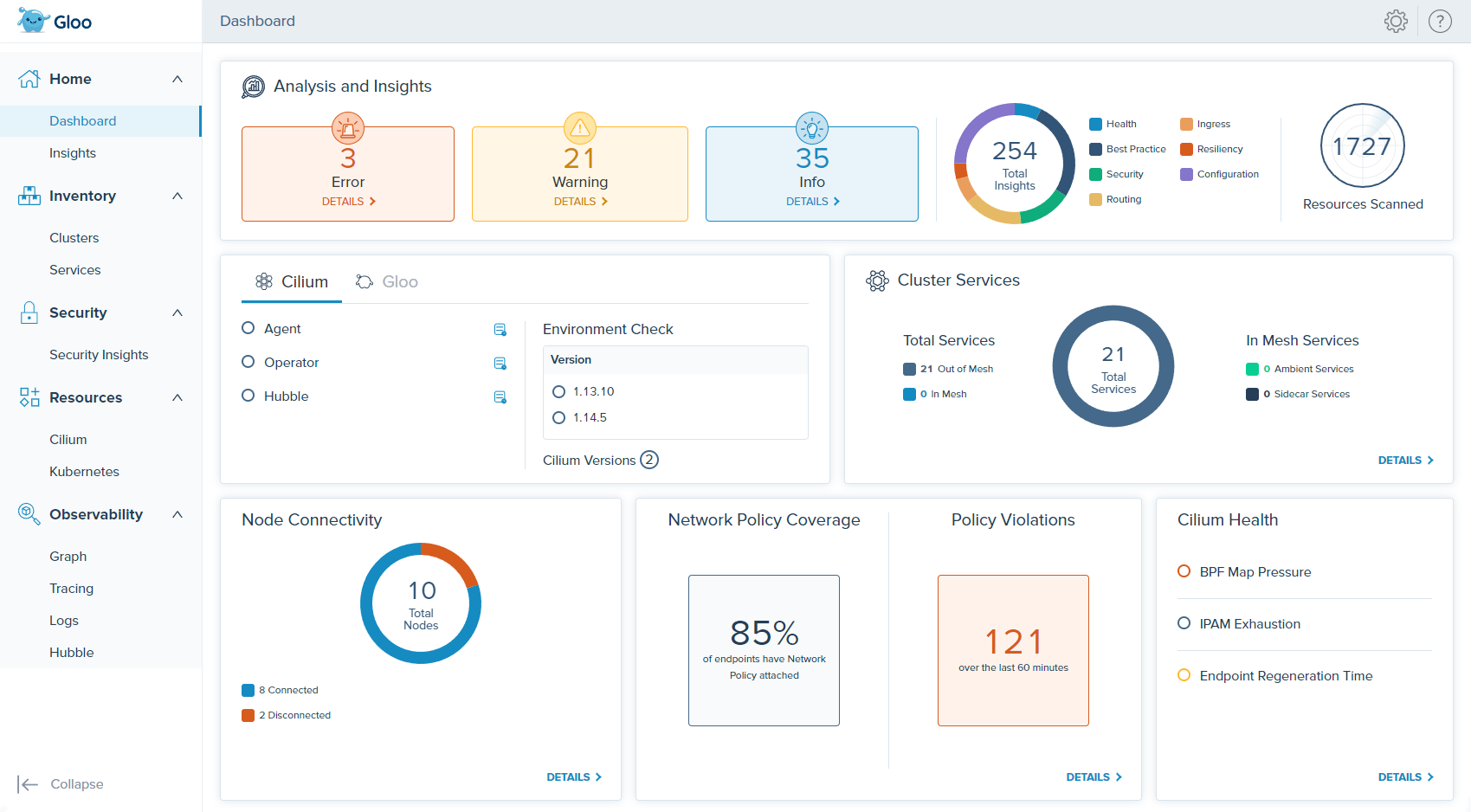
Gloo Network for Cilium At A Glance
How does it compare to upstream Cilium?
| Features | Upstream Cilium | Gloo Network for Cilium |
| IPv4 and IPv6 Kubernetes CNI | ||
| eBPF Datapath | ||
| NetworkPolicy and CiliumNetworkPolicy | ||
| L3/L4 Policy | ||
| DNS and Egress Policy | ||
| Multi-cluster routing, discovery, and security | ||
| Transparent encryption with IPSec and Wireguard | ||
| Prometheus and OpenTelemetry | ||
| Hubble observability | ||
| Cloud Provider Integration | ||
| Long term support (n-4) with 24x7 SLA | — | |
| Self-service operational insights for Cilium | — | |
| Multi-cluster observability | — | |
| Multi-cluster management plane | — | |
| Single pane of glass operational dashboard with RBAC | — | |
| Integration with Istio (sidecar) | — | |
| Integration with Istio Ambient (sidecarless) | — | |
| Download the Datasheet |
Gloo Network for Cilium is great for…
Vendor-Neutral Networking
Gloo Network is the leading vendor-neutral Cilium CNI for enterprises. It avoids vendor lock-in, granting flexibility and control over network infrastructures.

Streamlined Network Security
Advanced Layer 3/4 filtering and simplified CiliumNetworkPolicy management ensure secure, controlled network environments.
Enhanced Visibility and Monitoring
Offers extensive network observability, crucial for traffic monitoring, performance assessment, and anomaly detection. Integration with Hubble provides key insights for network troubleshooting and compliance.
Efficient Network Management
Simplifies configuration and optimizes resource use, reducing costs and complexity, especially in large-scale deployments.
Robust Security and Regulatory Compliance
Complies with stringent standards, featuring DNS-aware policies, FQDN policy, and IPsec encryption for secure networking in regulated industries.
Seamless Service Mesh Integration
Integrates with Gloo Mesh Core or Enterprise, adding security and observability layers, ideal for enterprise service mesh deployments.