
The Most Mature Envoy‑Based API Gateway
Kgateway delivers enterprise-grade performance with the flexibility of self-managed deployment. Run in your cloud, your way—with the same codebase powering Fortune 500 companies processing billions of API calls per day.


Trusted by industry leaders










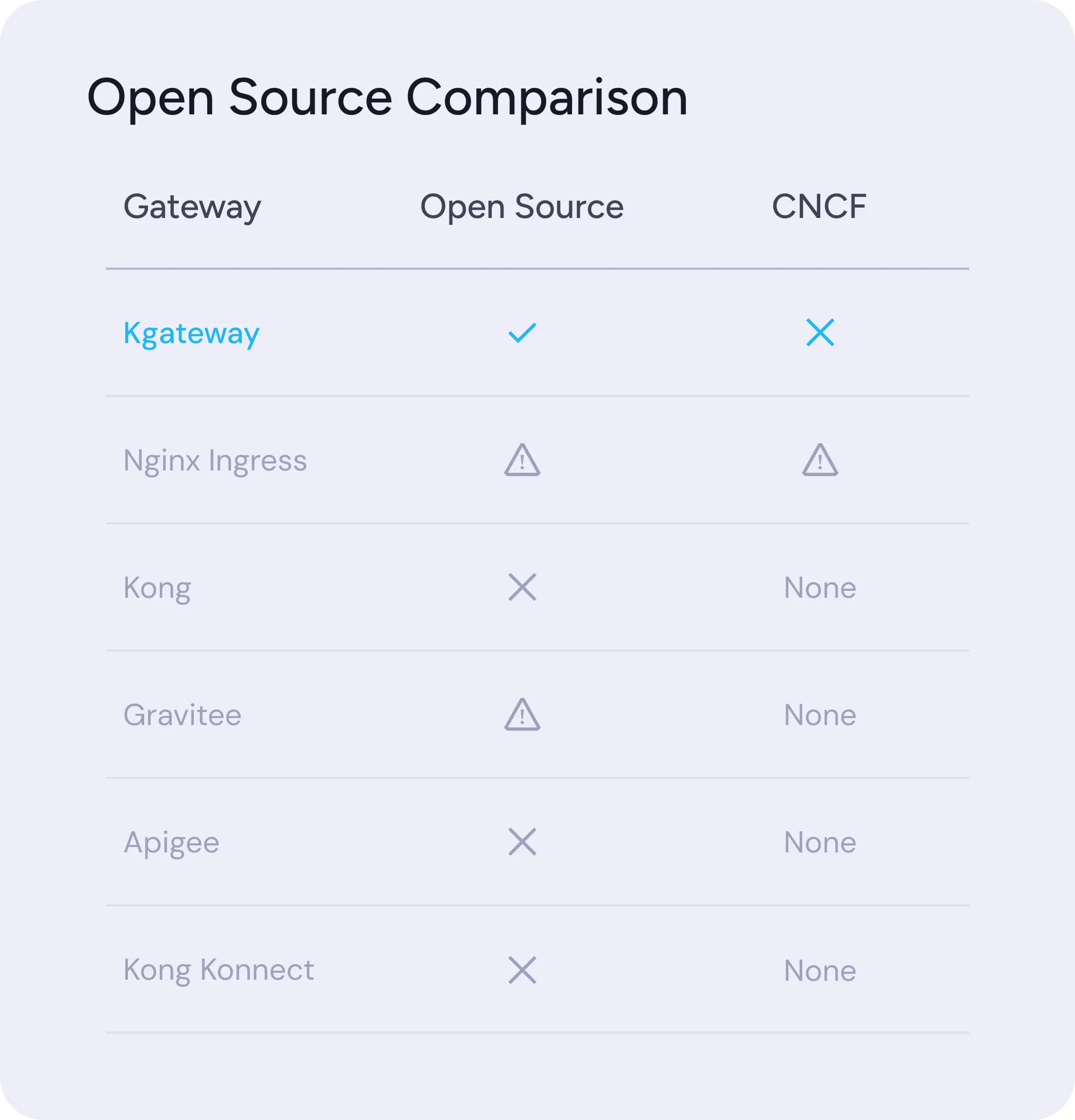
True Open Source. No Asterisks.
While other gateway vendors have retreated behind paywalls, or where continued maintenance is questionable, Kgateway remains committed to 100% open source under the CNCF. No bait-and-switch licensing. Fully featured with a diverse community, available Enterprise extensions when you're ready for them.
- CNCF Sandbox project with clear governance
- Apache 2.0 licensed—forever
- Active community with regular releases
- No vendor lock-in, Enterprise extensions only when you need them
Independent Benchmarks
The Best Gateway Performance at Scale
Independent testing from the gateway-api-bench project demonstrates Kgateway leadership across throughput, latency, and resource efficiency.

Solo Enterprise for Kgateway
Start Free. Scale with Enterprise Confidence
Kgateway open source is free forever. Add enterprise features and support when you need them.

24x7 Support SLA
Round-the-clock enterprise support with guaranteed response times.

N-3 Long Term Support
Extended support for previous versions with security patches and bug fixes.

FIPS Compliant Images
Hardened container images meeting federal security standards.

Private Slack Channel
White-glove support with direct access to Solo.io engineers.

Traffic Management
Intelligent Traffic Control for Modern Applications
Route, split, and transform traffic across any protocol—REST, gRPC, GraphQL, WebSocket, and more. Kgateway gives platform teams centralized control while enabling application teams to self-service their routing needs through delegation. From simple path-based routing to complex weighted canary deployments, handle it all with Kubernetes-native configuration.

Open Source
Request Routing
Route by path, header, method, query parameter, or host. Full Kubernetes Gateway API support.
Open Source
Traffic Splitting
Weighted routing for canary deployments, A/B testing, and progressive rollouts.
Open Source
Route Delegation
Delegate route configuration to application teams with multi-level delegation and policy inheritance.
Open Source
Header Manipulation
Add, remove, or modify request and response headers. Support for dynamic values.
Open Source
URL Rewrites
Rewrite paths, hosts, and query parameters. HTTP to HTTPS redirects.
Enterprise
Staged Transformations
Complex request/response transformations with templating. Extract, inject, and modify payloads.
Enterprise
AWS Lambda Integration
Seamless replacement for AWS API Gateway with automatic request and response translation.
Enterprise
Istio Ambient Integration
Ingress-to-mesh connectivity with Istio ambient mode for seamless service mesh integration.
Enterprise
Multicluster Routing
Multi-cluster traffic routing with service-level failover across Kubernetes clusters.

Security
Defense in Depth at the Edge
Protect your APIs with enterprise-grade security that scales. From TLS termination and mTLS to advanced authentication with OAuth 2.0/OIDC, JWT validation, and Web Application Firewall capabilities—Kgateway provides the security controls you need without slowing down development. Meet compliance requirements with FIPS-compliant images and data loss prevention policies.

Open Source
TLS Termination
Terminate TLS at the edge with automatic certificate management. SNI-based routing.
Open Source
mTLS
Mutual TLS for upstream, downstream, and service-to-service communications.
Open Source
CORS Protection
Cross-origin resource sharing policies. CSRF token validation.
Open Source
JWT Validation
Validate JWT tokens at the gateway. Extract claims for routing and authorization.
Enterprise
External Auth Service
Integrate with custom auth services. OPA policy enforcement. API key management.
Enterprise
Web Application Firewall
Monitor, filter, and block harmful HTTP traffic using ModSecurity rules and OWASP Core Rule Set.
Enterprise
Data Loss Prevention
Apply DLP masking to response bodies, headers, and access logs to protect sensitive data like credit cards and SSNs.
Enterprise
FIPS Compliance
FIPS-compliant images meeting NIST Federal Information Processing Standards for regulated environments.

Resiliency
Keep Services Running When Things Go Wrong
Build fault-tolerant systems with battle-tested resiliency patterns. Circuit breakers prevent cascade failures, retries with exponential backoff handle transient errors gracefully, and rate limiting protects your backends from overload. Whether it’s a traffic spike or a misbehaving downstream service, Kgateway keeps your APIs available and responsive.

Open Source
Retries and Timeouts
Configurable retry policies with exponential backoff. Per-route and per-try timeouts.
Open Source
Circuit Breakers
Outlier detection and ejection. Prevent cascade failures across services.
Open Source
Health Checks
Active and passive health checking. Automatic endpoint removal and recovery.
Open Source
Local Rate Limiting
Per-gateway rate limits. Token bucket algorithm with configurable fill rates.
Enterprise
Global Rate Limiting
Distributed rate limiting across gateway replicas. Rate limit by user, API key, or custom attributes.
Open Source
Traffic Mirroring
Shadow traffic to test new versions. Debug production issues safely.
Enterprise
Service-Level Failover
Ambient multicluster integration to detect failed services and maintain availability with failover routing.

Developer Portal
Accelerate API Adoption with Self-Service
Give developers everything they need to discover, understand, and integrate with your APIs. The Gloo Portal provides automatic API documentation from OpenAPI specs, self-service credential management, and customizable portal experiences. Reduce time-to-first-call and increase API adoption across your organization and partners.

Enterprise
API Discovery
Automatic discovery of OpenAPI specifications from services and external endpoints.
Enterprise
Portal Backend
Headless Portal REST API supports pluggable frontend portal UI integration.
Enterprise
Portal Frontend
Customizable web UI where developers discover and authenticate to your APIs.
Enterprise
API Products
Bundle and publish APIs with metadata, versioning, tags, and terms of service.
Enterprise
Self-Service
Self-service provisioning for API Keys and OAuth clients/service accounts to access protected APIs.
Enterprise
Secure Portal Access
Self-service request and approval workflows for API product access across developers and partners.

Analytics & Monetization
Turn API Traffic into Business Insights
Understand how your APIs are being used and by whom. Track usage patterns, identify your most valuable consumers, and make data-driven decisions about your API strategy. With built-in monetization capabilities, transform your APIs from cost centers into revenue streams with usage-based billing and tiered access plans.

Enterprise
API Usage Analytics
Track total requests, error rates, consumers, and services with detailed usage dashboards.
Enterprise
Usage Plans
Create and manage usage plans with rate limits and access controls for API products.
Enterprise
Monetization
Persist API usage data to monetize APIs based on actual consumption patterns.
Enterprise
Usage Graphs
Visualize API usage data with graphs in the Admin Dashboard for insights and reporting.
Enterprise
Consumer Tracking
Track requests by user, email, or API key to understand consumer behavior.
Enterprise
Grafana Dashboards
View usage information through integrated Grafana dashboards with OpenTelemetry pipeline.

AI, MCP, and Agents
Secure, Govern, and Observe Your AI Infrastructure
Traditional API gateways weren't built for AI—they're optimized for stateless REST interactions, not the stateful, bidirectional, session-aware patterns that LLMs, MCP, and agents demand. That's why Solo built Agentgateway from the ground up: a high-performance Rust-based gateway purpose-built for the agentic era. Now a Linux Foundation project, Agentgateway is to AI infrastructure what Envoy became for cloud-native—the foundational data plane for secure, observable, enterprise-grade AI connectivity.

AI Gateway
Centralize API keys, enforce guardrails on every prompt and response, and get complete visibility into LLM usage and costs. A unified API lets you swap providers without touching application code—optimize for performance, availability, or price on the fly.
MCP Gateway
MCP servers can dynamically request backend URLs—creating shadow access that bypasses security. Validate, sandbox, and observe every tool call from a single control point. Turn existing REST APIs into MCP tools instantly using their OpenAPI spec with zero custom code.
Inference Gateway
Context-aware routing that directs traffic to the right model—including fine-tuned variants. Maximize GPU utilization with smart routing to inference pools. Isolate prefill and decode stages to extract maximum efficiency from expensive accelerators and slash time-to-first-token.
Discover more
Resources to help you succeed with kgateway.

