Solo Enterprise for agentgateway 2.2 is now generally available, built on agentgateway OSS 1.0. This release focuses on a problem every developer using AI coding agents has hit: authentication pop-ups breaking your flow mid-task. Agentgateway 2.2 solves this by authenticating users up front when they connect, so MCP tool calls just work without interruption.
Beyond MCP authentication, 2.2 delivers Anthropic protocol translation, cloud-native prompt guards, richer LLM cost visibility, and significant MCP security hardening - across both the open-source and enterprise editions.
Seamless MCP Authentication for Desktop AI Agents
The problem
Today, most developers run MCP servers locally on their laptops, no authentication required. But that's changing fast. As enterprises move toward shared, hosted MCP servers (think Atlassian, GitHub, or internal platform services), those servers require login. And that's where the experience breaks down.
Picture what happens when your team moves to hosted MCP: a developer is deep in a coding session in Cursor or Claude Code, their agent calls a tool, and an OAuth pop-up interrupts everything. They authenticate with the SaaS provider, the agent retries, and maybe it works, or maybe the context is lost and they start over. Multiply that across every provider and every session, and the agentic experience falls apart.
For enterprises, the problem goes deeper than developer friction. Each SaaS MCP provider has its own identity system, and ad-hoc OAuth flows mean developers are authenticating directly with GitHub, Atlassian, or Google - bypassing corporate SSO entirely. IT loses visibility and audit trails have gaps. On top of that, the OAuth scopes offered by SaaS providers are a bad match for MCP - "read/write all repositories" when you really want to give access to the list_repositories tool, for example. Enterprises need to provide fine-grained policies: controlling not just which providers developers can reach, but which MCP tools they're allowed to use.
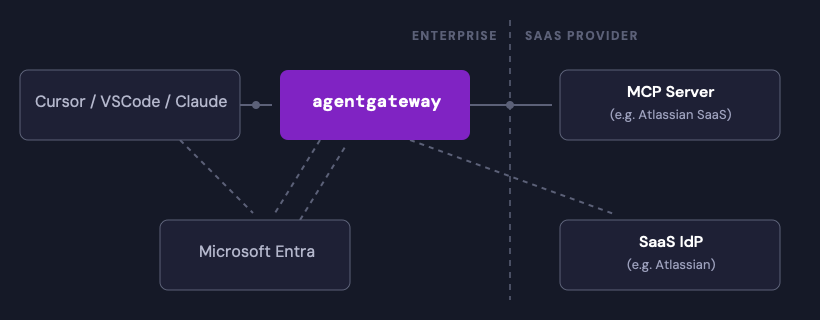
The solution: authenticate at connect time
With agentgateway 2.2, when a user connects to the gateway the full login flow runs immediately: enterprise SSO first, then token exchange to the upstream SaaS IdP (GitHub, Atlassian, Google, etc.). Tokens are stored at the gateway. From that point on, tool calls just work - no interruptions, no pop-ups.
This is more than a convenience improvement. It means:
- Enterprise SSO is enforced on every MCP connection, not bypassed by direct SaaS access
- Fine-grained access policies control which OAuth scopes each agent can request, layering authorization on top of identity - conforming to the MCP spec and overcoming limitations of raw OAuth scopes
- Two modes, one gateway - authenticate at connect time for desktop agents, or use MCP elicitation for autonomous agents and multi-hop chains that need deferred user consent
For the full deep-dive on the authorization patterns, SaaS MCP scenarios, and how agentgateway prevents bypass, read Christian Posta's blog: Connecting SaaS MCP Servers to Enterprise with agentgateway.
What Else Is New
Anthropic Messages API Translation
The gateway now accepts Anthropic /v1/messages requests and translates them bidirectionally to and from OpenAI /v1/chat/completions format. Clients using the Anthropic SDK can send requests through agentgateway to any OpenAI-compatible backend—OpenAI, Azure OpenAI, Vertex AI, Gemini—without changing client code. The gateway auto-detects the input format from the request path.
Cloud-Native Prompt Guards
New prompt guard integrations with AWS Bedrock Guardrails and Google Model Armor let you block PII, prompt injection, and unsafe content on both request and response paths. Up to eight guards can be configured per direction, and both providers work alongside existing regex and webhook guards in the same policy.
LLM Cost Visibility
Token usage telemetry now includes reasoning_tokens, cached_input_tokens, and cache_creation_input_tokens. These fields are available in CEL expressions, metrics, and access logs — giving operators visibility into the LLM costs that were previously invisible at the gateway layer. You can now identify which requests consume expensive reasoning budgets and measure whether your prompt caching is actually working.
LLM Request Transformations
A new transformations policy lets you use CEL expressions to modify LLM request bodies before they reach the backend. Cap max_tokens, inject system prompts, or normalize parameters across providers — all at the gateway layer.
MCP Security Hardening
Several important changes strengthen MCP security posture:
- Strict authentication by default - MCP backends now reject unauthenticated requests unless you explicitly opt into permissive mode
- Per-request policy evaluation - authorization policies take effect immediately when updated, without requiring clients to re-establish MCP sessions
- Deny-only policy fix - a critical correctness bug was fixed where deny-only authorization policies were incorrectly blocking all tools instead of just the specified ones
- CORS before auth - CORS evaluation now runs before authentication and rate limiting, fixing browser preflight failures that made cross-origin MCP access impossible when auth was enabled
Microsoft Entra Token Exchange
Enterprise policies now support per-backend token exchange using Microsoft Entra's On-Behalf-Of (OBO) flow, enabling seamless proxy of user tokens to backend-specific tokens for services like Azure Kubernetes Service.
Infrastructure and Gateway API
- Gateway API 1.5.0 - XListenerSet promoted to ListenerSet, mTLS AllowInsecureFallback, CORS wildcard support
- GRPCRoute support - route traffic to gRPC endpoints through agentgateway
- Controller autoscaling - HPA and VPA policies for the agentgateway control plane
- Static IP addresses for Gateway services
- Priority classes and common labels for better operational control
For the full list of changes, see the release notes. For a detailed comparison of OSS and enterprise features, see the feature matrix.
What's Next
MCP Authentication and Secrets Management
The MCP authentication capabilities in 2.2 are just the beginning. In 2.3, we're extending them with secure external secrets storage - integrating with systems like HashiCorp Vault so that OAuth credentials and tokens don't need to live in Kubernetes secrets. We're also simplifying the OAuth configuration API to reduce the boilerplate required to onboard new SaaS MCP providers. The goal: make MCP authentication truly production-ready for enterprises managing dozens of SaaS integrations.
And beyond
Further out, we're working on running agentgateway outside of Kubernetes, semantic caching for LLM requests, automatic exposure of OpenAPI endpoints as MCP tools, BYO ClickHouse for observability, and defining reusable skills at the gateway layer. Stay tuned.
Get Started
- Product page - learn more about Solo Enterprise for agentgateway
- Free trial - try agentgateway in your environment
- agentgateway OSS on GitHub - star the repo, open issues, contribute




























%20a%20Bad%20Idea.png)











%20For%20More%20Dependable%20Humans.png)
