Solo Enterprise for Istio
From microservices to agents. One mesh for everything at any scale
Your platform spans clouds, clusters, and now agentic workloads. Solo Enterprise for Istio extends Ambient Mesh to meet all of it — one control plane from microservices to MCP.
Multicluster Peering
Two architectures.
One seamless mesh.
Gateway-routed mTLS peering across VPCs and clouds — no shared secrets. Direct pod-to-pod flat networking within a VPC for minimal latency. Mix both per cluster pair.
No API Server Access
Sub-100ms Propagation
Resilient By Design

Global Service Discovery
One Global service name. Any cluster. Any instance.
Stop hardcoding cluster endpoints. With Solo Enterprise for Istio, every service is reachable from everywhere — automatic routing to the nearest healthy instance.
curl http://orders.mesh.internal/api/v1/status
# Automatic routing to nearest healthy instance
# across us-east-1, eu-west-1, or ap-south-1
No Gateway Hops
Automatic Failover
Unified Namespace

Node-based L7 Observability
HTTP visibility.
Without the overhead.
Get full Layer 7 observability — HTTP methods, paths, response codes, and traces — directly from the node proxy. No waypoints required. No per-service sidecars. Just instant visibility with near-zero performance impact.
Ultra-High Performance
Safety First Design
Full L7 Metrics

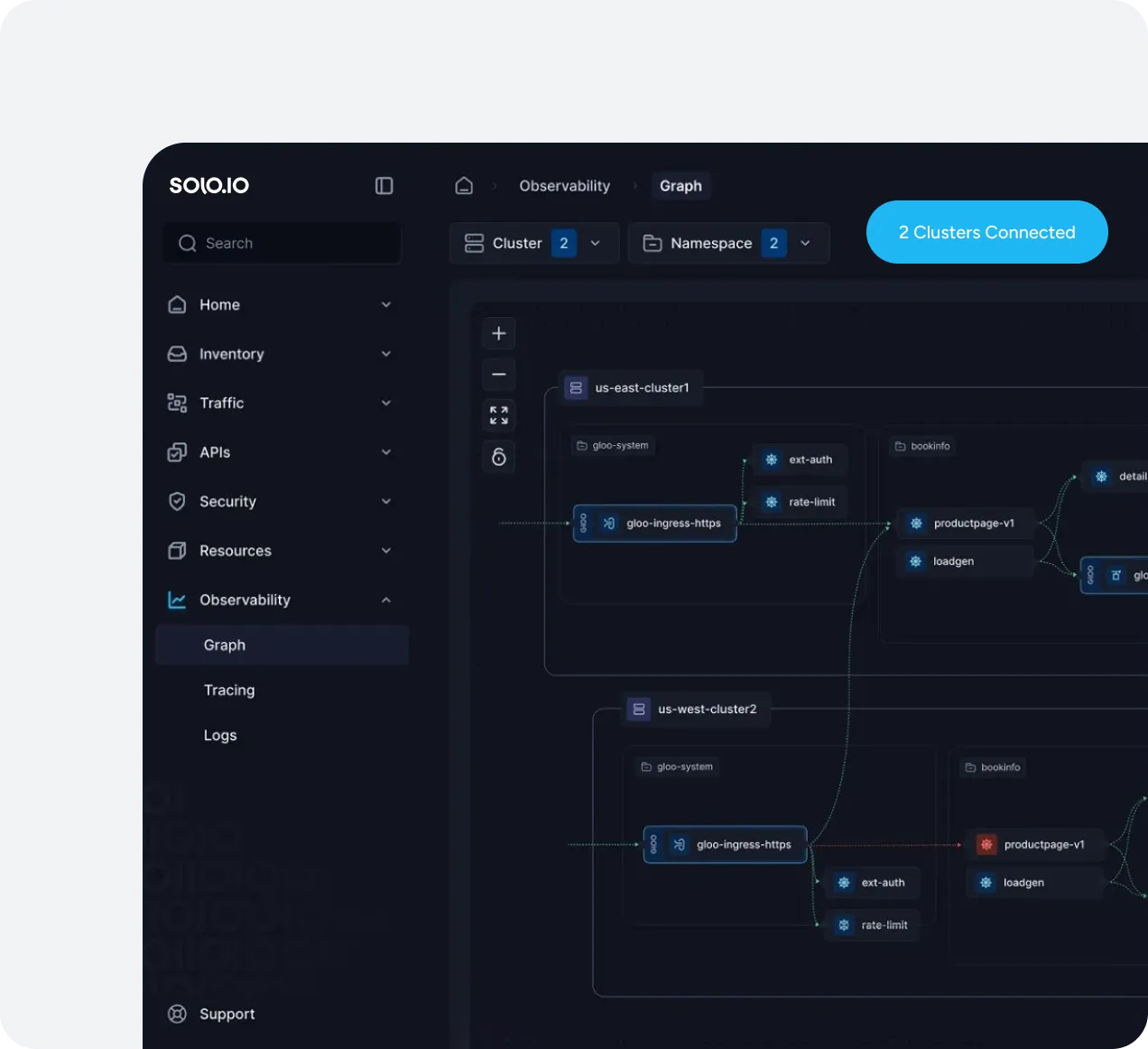
Multicluster Peering
See everything.
Across every cluster.
Unified service graph, tracing, and metrics across all your clusters. Understand traffic flows, identify bottlenecks, and troubleshoot issues — all from a single pane of glass.
Real-Time Service Graph
Application Metrics Without Sidecars
Distributed Tracing
Segments
Your org structure.
Every tenant.
In your mesh.
Segments partition a mesh into logical boundaries that match how your teams actually work. Each segment gets its own domain — so mesh.platform, mesh.alpha, and mesh.bravo resolve independently, even with identical service names.
Team Isolation
Multi-Cluster, One Team
Shared Platform Services

Runtime Extensions
Beyond Kubernetes.
Into your entire stack.
Extend your ambient mesh to workloads running anywhere — Amazon ECS containers, virtual machines, or legacy infrastructure. One unified mesh with mTLS security, traffic management, and observability across all your runtimes.
Amazon ECS Integration
Virtual Machine Support
AWS Lambda & Serverless
Unified Security & Policies

SPIRE Integration
Identity you can prove. Not just assert.
Replace Istio's default identity model with SPIRE's hardware-rooted workload attestation. Every mTLS certificate is backed by cryptographic proof — not just a Kubernetes service account.
Node Attestation
Zero Pod Changes
Multicluster Ready

Agent Mesh
Your mesh just learned
to speak AI.
Deploy agentgateway as a waypoint proxy in Ambient Mesh. Get native MCP and A2A protocol awareness, context-aware security policies, and full agentic observability — all enforced by the mesh so no client can bypass it.
Context-Aware AuthZ
Native Protocol Support
Rust-Powered Performance
Mesh-Enforced Security


Discover more
Resources to help you succeed with Istio and Ambient Mesh.